PESCAN.IO - Analysis Report Basic |
|||||||
| File Structure |
|
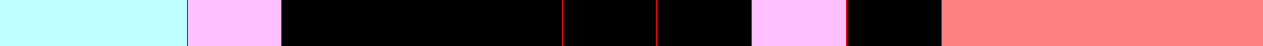
PE Chart Code
Header PE (light blue)
Executable sections (pink)
Non-executable sections (black)
External injected code (red)
File Structure in red = malformed or corrupted header
Chart Code For Other Files
Printable characters (blue)
Non-printable characters (black)
| Information |
| Size: 6,74 KB SHA-256 Hash: CE5B7AAD9B51A3DF9BBAFF5526C1ADDCB844ED7AEB1FCA368D7B41462F6333A7 SHA-1 Hash: 0B1DD0B32B8056302D7151182E06788CEFA89978 MD5 Hash: B69D358DD6971F7969942576E85CDC7F Imphash: 153145B9975A097E9B9F0BC04730FFD7 MajorOSVersion: 10 MinorOSVersion: 0 CheckSum: 0000AA62 EntryPoint (rva): 1000 SizeOfHeaders: 400 SizeOfImage: 7000 ImageBase: 0000000140000000 Architecture: x64 ImportTable: 5000 IAT: 2000 Characteristics: 22 TimeDateStamp: 6792048C Date: 23/01/2025 8:57:48 File Type: EXE Number Of Sections: 6 ASLR: Disabled Section Names (Optional Header): .text, .rdata, .data, .pdata, INIT, .reloc Number Of Executable Sections: 2 Subsystem: Native |
| Sections Info |
| Section Name | Flags | ROffset | RSize | VOffset | VSize | Entropy | Chi2 |
|---|---|---|---|---|---|---|---|
| .text | 0x68000020 Code Shared Executable Readable |
400 | 200 | 1000 | 144 |
|
|
| .rdata | 0x48000040 Initialized Data Shared Readable |
600 | 600 | 2000 | 408 |
|
|
| .data | 0xC8000040 Initialized Data Shared Readable Writeable |
C00 | 200 | 3000 | 10 |
|
|
| .pdata | 0x48000040 Initialized Data Shared Readable |
E00 | 200 | 4000 | 3C |
|
|
| INIT | 0x62000020 Code GP-Relative Executable Readable |
1000 | 200 | 5000 | 6A |
|
|
| .reloc | 0x42000040 Initialized Data GP-Relative Readable |
1200 | 200 | 6000 | 24 |
|
|
| Entry Point |
The section number (1) have the Entry Point Information -> EntryPoint (calculated) - 400 Code -> 488954241048894C24084883EC28488D0D1B010000E878000000488B442430488D0D1A00000048894868E83100000033C048 Assembler |MOV QWORD PTR [RSP + 0X10], RDX |MOV QWORD PTR [RSP + 8], RCX |SUB RSP, 0X28 |LEA RCX, [RIP + 0X11B] |CALL 0X1092 |MOV RAX, QWORD PTR [RSP + 0X30] |LEA RCX, [RIP + 0X1A] |MOV QWORD PTR [RAX + 0X68], RCX |CALL 0X1060 |XOR EAX, EAX |
| Signatures |
| Rich Signature Analyzer: Code -> B510ABFBF171C5A8F171C5A8F171C5A885F0C4A9F271C5A8F171C4A8F371C5A885F0C6A9F371C5A885F0C1A9F571C5A8B9F4C0A9F071C5A8B9F4C7A9F071C5A852696368F171C5A8 Footprint md5 Hash -> 84681AA24459F2B9CACDA32E9F48377B • The Rich header apparently has not been modified |
| Packer/Compiler |
| Compiler: Microsoft Visual Studio Detect It Easy (die) • PE+(64): linker: Microsoft Linker(14.41**)[-] • PE+(64): Sign tool: Windows Authenticode(2.0)[PKCS 7] • Entropy: 3.93358 |
| File Access |
| ntoskrnl.exe .dat H.dat |
| Interest's Words |
| RootKit |
| Strings/Hex Code Found With The File Rules |
| Rule Type | Encoding | Matched (Word) |
|---|---|---|
| Text | Ascii | Software designed to enable unauthorized access while hiding its presence (Rootkit) |
| Text | Ascii | Technique used to circumvent security measures (Bypass) |
| Entry Point | Hex Pattern | Microsoft Visual C++ 8 |
| Entry Point | Hex Pattern | Microsoft Visual C++ 8.0 |
| Entry Point | Hex Pattern | Microsoft Visual C++ 8.0 (DLL) |
| Intelligent String |
| • C:\Users\victim\Documents\GitHub\ComodoBypassRootkit\ComodoBypassRootkit\ComodoBypassRootkit\x64\Debug\ComodoBypassRootkit.pdb • ntoskrnl.exe |
| Flow Anomalies |
| Offset | RVA | Section | Description |
|---|---|---|---|
| 486 | N/A | .text | CALL QWORD PTR [RIP+0xF74] |
| 492 | N/A | .text | JMP QWORD PTR [RIP+0xF70] |
| 4E0 | N/A | .text | JMP QWORD PTR [RIP+0xF3A] |
| 1400 | N/A | *Overlay* | F806000000020200308206EA06092A864886F70D | ........0.....*.H... |
| Extra Analysis |
| Metric | Value | Percentage |
|---|---|---|
| Ascii Code | 2019 | 29,2439% |
| Null Byte Code | 4143 | 60,0087% |
© 2026 All rights reserved.